Think of your APIs less like gateways and more like the nervous system of your company. Every mobile integration, partner workflow, internal service call, and automated transaction flows through them and with that comes a critical reality: your APIs don't just expose data anymore. They encode the operational logic of the business itself.
That shift changes the threat landscape fundamentally.
The most damaging vulnerabilities in modern systems are no longer injection flaws. Those matter, but the breaches making headlines today are far more subtle. They live in the logic that governs how identities interact with objects, and how workflows are supposed to be enforced. When that logic breaks or worse, when it's never consistently enforced to begin with, the consequences can be severe.
Two categories sit at the center of this problem: Broken Object Level Authorization (BOLA) and business logic vulnerabilities. Both arise when applications fail to enforce who can access which objects, and under what conditions actions can occur. They don't look like coding mistakes. They only emerge when a system is exercised through real interactions, across real identities, objects, and workflows.
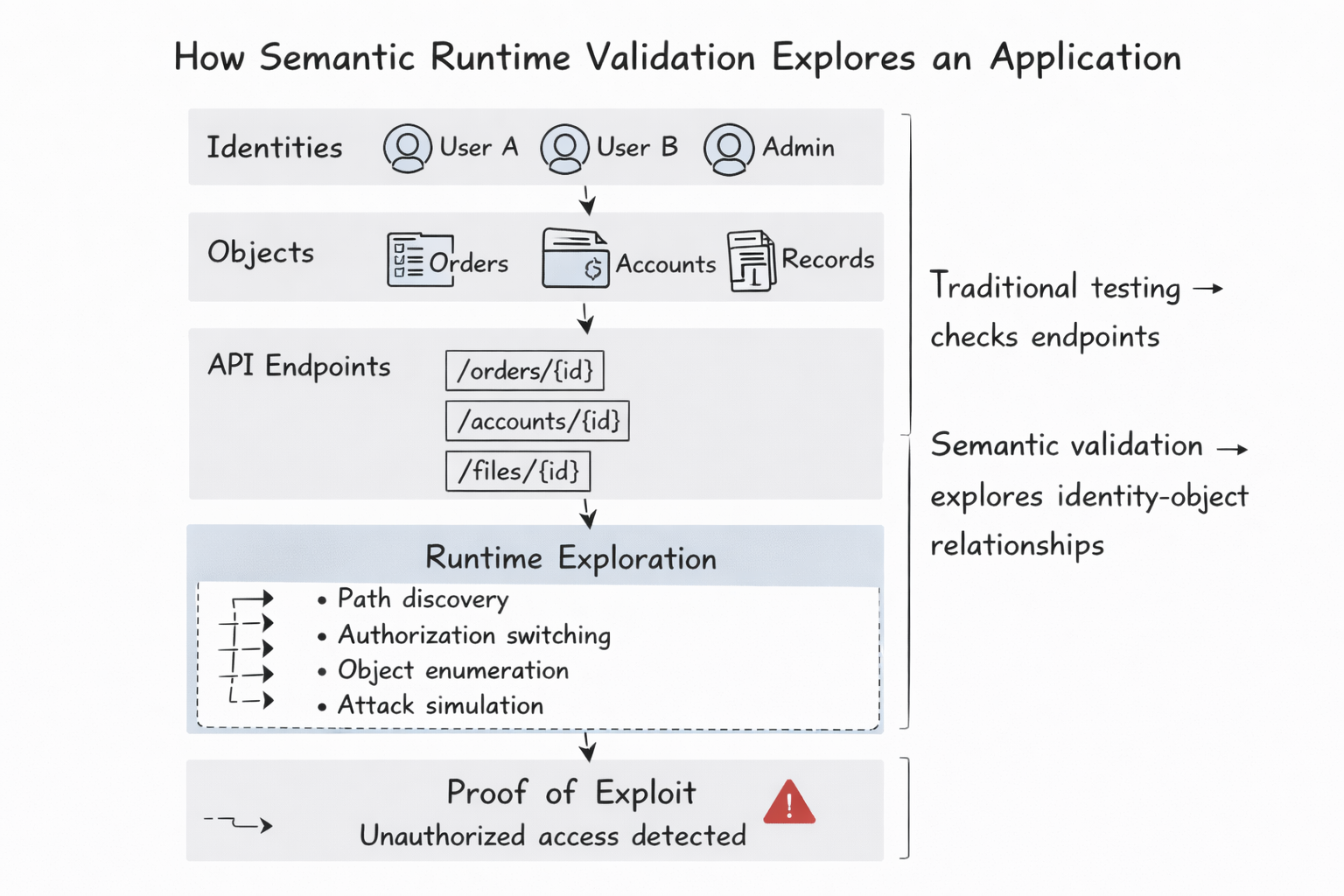
Detecting them requires observing how the application behaves at runtime. That is precisely the purpose of Semantic Runtime Validation.
The Challenge of API Attack Paths
Modern attackers don't kick the door down with a SQL injection. They're more like digital locksmiths, trying a sequence of keys in a specific order until the tumblers click. They explore a system through chains of legitimate-looking API interactions, each one revealing a little more about how identities, objects, and permissions relate to each other.
Traditional security testing methods aren't designed to follow these paths.
Static analysis (SAST) inspects source code for insecure constructs, it's like studying a blueprint to find a weak wall. Dynamic scanning (DAST) probes endpoints with predefined payloads, closer to throwing a rock at a window. Manual penetration testing covers more ground but typically focuses on a limited number of endpoints and known techniques.
None of these approaches catch the attacker who walks in calmly, presents a valid-looking credential, and asks for something they have no right to, because each individual step appears legitimate
BOLA and business logic vulnerabilities rarely appear in this conventional testing because they do not arise from malformed inputs or obvious coding errors. They emerge from the behavioral relationships between identities and objects unfolding across multiple API interactions.
Semantic Runtime Validation focuses on these behaviors. Instead of testing endpoints in isolation, it analyzes how APIs behave when executed as part of complete interaction flows. The system observes how identities interact with objects, how workflows evolve, and how permissions are enforced across services.
This approach reveals vulnerabilities that only appear when requests are evaluated in context.
Modeling Object Ownership
Most APIs expose resources such as accounts, orders, invoices, documents, projects, and messages. These objects are typically associated with specific identities. Security depends on consistently enforcing that the correct identities can access or modify the correct objects.
In practice, this is harder than it sounds. In a distributed microservices architecture, the question "who actually owns Order #504?" can get surprisingly blurry. Service A may assume Service B validated the identity. Service B may assume the check already happened upstream. Neither is wrong in isolation, but together, they create a gap.
Semantic Runtime Validation doesn't rely on pre-written rules to catch this. It watches the application running in real time, learning from observed behavior: which identities create which objects, how those objects are referenced, and what access patterns look normal. It builds a live ownership map from these observations.
Once that map exists, it starts testing boundaries. If an identity can retrieve, modify, or delete an object that falls outside its expected scope, that's a Broken Object Level Authorization vulnerability. The flaw is revealed not through static code inspection, but through inconsistencies in runtime behavior.
Identity Switching
Many authorization flaws remain completely invisible when applications are tested under a single identity. A user interacting with their own data will never encounter an ownership violation, because they have no reason to try accessing someone else's.
Semantic Runtime Validation addresses this systematically through identity switching. Interactions observed under one identity are replayed under others to determine whether the system correctly enforces access boundaries.
This surfaces two critical classes of authorization failure:
- Horizontal privilege escalation: one user gaining access to another user's data
- Vertical privilege escalation: a lower-privileged user performing actions intended only for administrators or service accounts
Think of it like checking every door in a hotel to confirm your key opens Room 204, and only Room 204. Because identity switching occurs across realistic interaction flows, the findings represent actual exploit paths, not theoretical weaknesses.
Authorization Graph Validation
Authorization logic in modern systems rarely lives in one place. It emerges from the interaction of authentication tokens, role assignments, ownership attributes, policy engines, and service-to-service trust relationships. Together, these form what can be described as an authorization graph.
Each node represents an identity, role, or object. Each edge represents a permission relationship or trust assumption. When an API request flows through the system, it traverses this graph, relying on various services to validate permissions and execute operations in the correct order.
In complex architectures, this graph almost always contains inconsistencies. One service enforces a permission that another assumes has already been checked. A workflow correctly denies access through one endpoint while inadvertently exposing the same capability through another. In 2026-scale systems, these gaps are too numerous and interconnected for humans to catch through review alone.
Semantic Runtime Validation reconstructs this authorization graph by observing how authorization decisions happen during actual runtime interactions. Once the graph is understood, the system tests whether the relationships within it are enforced consistently across every path.
If a user can't access an object directly but can modify it through a less-guarded service endpoint, that inconsistency becomes visible. These authorization gaps are nearly impossible to detect through traditional scanning because they only appear through the interaction of multiple services.
Detecting Business Logic Vulnerabilities
Not every critical vulnerability involves a broken authorization check. Many arise from failures to enforce the workflow rules that the application was designed to uphold.
Modern applications are built on assumptions about sequence. Transactions must be authorized before settlement. Approvals must precede execution. Certain states must be reached before further actions are permitted. These rules are often enforced at the application layer, but if an attacker can call the wrong endpoint in the wrong order, and the system just says "okay," the entire workflow has been bypassed.
Each individual endpoint may behave correctly in isolation. The vulnerability only appears when operations are executed in an unexpected sequence.
Semantic Runtime Validation detects these flaws by exploring alternative interaction paths and evaluating how the system responds to out-of-order workflows. It's the equivalent of trying to finish a marathon without running the first ten miles, and checking whether anyone notices.
In environments where AI code generation is changing the economics of AppSec, these sequential logic flaws are appearing faster than any periodic testing programme can track - and the alert fatigue multiplier effect makes them even harder to isolate from the noise.
Example: Detecting BOLA and Workflow Violations in Practice
Consider a simplified API-driven system that manages customer orders and financial transactions.
BOLA Scenario
A user retrieves an order belonging to their account.
GET /api/orders/123
Authorization: Bearer userA_token
The request succeeds because the order belongs to User A.
If the same user modifies the object identifier and attempts to retrieve another order:
GET /api/orders/124
Authorization: Bearer userA_token
…The request should fail because Order 124 belongs to User B.
If the system returns the order instead of rejecting the request, the application contains a Broken Object Level Authorization vulnerability. The system has failed to enforce object ownership boundaries.
Semantic Runtime Validation detects this by learning the ownership relationships between identities and objects and then systematically testing whether those relationships can be violated through alternate requests.
Identity Switching
After observing that User A created or accessed Order 123, the system attempts the same interaction using another identity.
GET /api/orders/123
Authorization: Bearer userB_token
If the request succeeds, the application allows horizontal privilege escalation, enabling users to access objects owned by other users.
Business Logic Scenario
Now consider a financial transaction workflow where the expected sequence is:
- Create transaction
- Authorize transaction
- Settle transaction
A correctly implemented workflow requires authorization before settlement.
Create transaction:
POST /api/transactions
Authorize transaction:
POST /api/transactions/981/authorize
Settle transaction:
POST /api/transactions/981/settle
But if the system allows settlement to occur directly without authorization:
POST /api/transactions/981/settle
..the workflow has been bypassed. This is a business logic vulnerability because the system fails to enforce the required sequence of operations.
Semantic Runtime Validation detects this by exploring alternate execution paths and validating whether workflow state transitions are enforced or merely assumed.
Why Runtime Semantics Matter
BOLA and business logic vulnerabilities rarely reveal themselves through code inspection or signature-based scanning. They arise from the interaction of identities, objects, services, and workflows; and they only become visible when that system is actually running.
In an era of AI-driven development and autonomous agents, "set it and forget it" security is no longer viable. Code changes daily. Attackers now increasingly operate through autonomous systems that can infer business logic and chain together legitimate-looking requests into adaptive exploits.
Proving security requires validating the behavior of a living system, not just the static files in a repository.
Semantic Runtime Validation focuses on observing and validating these behaviors. By modeling object ownership, switching identities, analyzing API attack paths, and validating authorization graphs, it exposes vulnerabilities that exist where attackers actually operate.
Not in source code alone.
But in the behavior of running systems.
That's not a one-time test. It's continuous proof.
For modern API-driven architectures, proving security requires validating that behavior continuously. That is the role of Semantic Runtime Validation.
The 2026 CISO Checklist: Defending the Logic Layer
Take control of your Application and API security
See how Aptori’s award-winning, AI-driven platform uncovers hidden business logic risks across your code, applications, and APIs. Aptori prioritizes the risks that matter and automates remediation, helping teams move from reactive security to continuous assurance.
Request your personalized demo today.


%20(1).png)






