Why Behavioral Security Validation Is Replacing Traditional Scanning
Application security is entering a structural transition.
For nearly two decades, security programs have focused on identifying vulnerabilities through static code analysis, dynamic scanning, and periodic penetration testing. These methods were designed for a different generation of software. Applications were monolithic, user interfaces were web pages, and most security issues involved well understood input validation flaws.
That world no longer exists.
Modern applications are built around APIs, microservices, and identity driven workflows. Authorization decisions span services. Data relationships cross tenants. Application logic is distributed across dozens of components that communicate through service interfaces rather than web forms.
In this environment, many of the most damaging vulnerabilities no longer originate from simple coding mistakes. Instead they arise from how systems behave.
Attackers exploit gaps in authorization logic, inconsistencies in object ownership enforcement, and subtle weaknesses in application workflows. These vulnerabilities cannot be reliably detected by scanning source code or fuzzing inputs.
The future of application security therefore requires a different approach. Security systems must move beyond pattern detection and begin validating whether applications actually behave securely during execution.
This shift is the foundation of Semantic Runtime Validation.
Why Traditional Application Security Testing Is Reaching Its Limits
The traditional application security stack consists of three primary techniques.
Static Application Security Testing analyzes source code to identify known vulnerability patterns. Dynamic scanners interact with applications at runtime to probe inputs and responses. Penetration testing introduces human expertise to discover complex issues.
Each technique still provides value. However, all three share a fundamental limitation.
They struggle to understand application behavior.
Static analysis tools examine code structure but cannot determine how systems behave during execution. Dynamic scanners fuzz inputs but rarely maintain state across workflows. Manual testing can uncover behavioral flaws, but it is constrained by time and scale.
Modern attacks increasingly target vulnerabilities that exist only when applications are exercised through realistic interactions across APIs and services.
For example, an API may correctly validate input fields and sanitize requests, yet still expose a critical vulnerability if object ownership is not enforced correctly. A user might simply change an identifier in a request and access data belonging to another user.
This vulnerability class, known as Broken Object Level Authorization, has become one of the most common API security issues in modern systems.
These types of flaws are not syntax problems. They are semantic problems.
Traditional scanners look for patterns in code. Attackers exploit relationships between users, objects, and workflows.
This mismatch between how scanners analyze systems and how attackers exploit them is widening as application architectures grow more complex.
The Shift from Syntax Based Security to Semantic Security
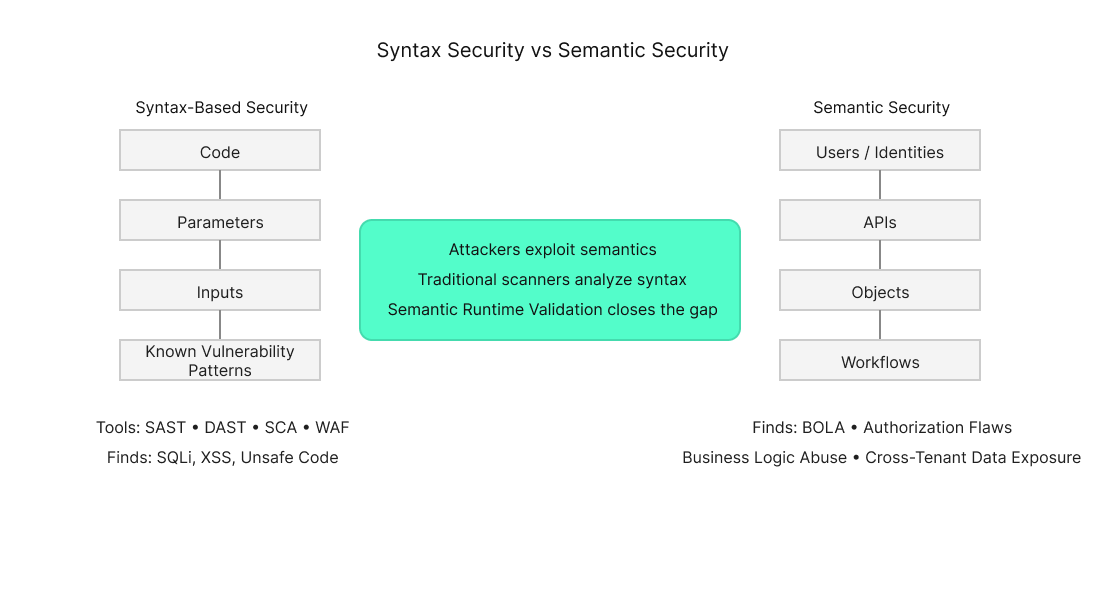
Most traditional security testing approaches are based on syntax.
They analyze code statements, parameters, and patterns that resemble known vulnerabilities such as injection attacks or insecure configuration settings.
However, modern application attacks often exploit the meaning of operations rather than their syntax.
Consider a typical API interaction.
A user authenticates, retrieves a list of objects, and requests details for a specific resource. Each individual request may be technically valid. The vulnerability occurs when the system fails to verify that the requesting user actually owns the object being accessed.
From a syntactic perspective, nothing appears wrong. The request is well formed, the parameters are valid, and the application responds correctly.
From a semantic perspective, the system has violated its own authorization rules.
Semantic Runtime Validation focuses on this behavioral layer. Instead of analyzing code structure or fuzzing parameters, it evaluates whether the relationships between identities, objects, and workflows enforce the intended security model.
What Is Semantic Runtime Validation?
Semantic Runtime Validation is an application security testing approach that analyzes how systems behave during execution and verifies whether those behaviors can be exploited.
Rather than relying solely on static rules or signature based scanning, Semantic Runtime Validation constructs a behavioral model of the application.
This model captures the relationships between several core elements.
Identities represent users, services, and authentication tokens interacting with the system. APIs define the operational interface through which identities access application functionality. Objects represent the data entities exposed by those APIs. Workflows represent the sequences of operations that implement business processes.
By understanding how these elements interact, the system can explore whether application behavior violates expected security constraints.
For example, it can evaluate whether a user can access objects belonging to another user, whether certain API operations bypass authorization checks, or whether a sequence of legitimate operations can be combined to manipulate a workflow.
These tests reveal vulnerabilities that emerge from application semantics rather than coding syntax.
Detecting Modern Vulnerabilities: BOLA, Authorization Flaws, and Business Logic Abuse
Many of the most serious vulnerabilities affecting modern APIs fall into categories that traditional scanners struggle to detect.
Broken Object Level Authorization vulnerabilities occur when applications expose object identifiers but fail to verify ownership. A user may simply modify an identifier in an API request to retrieve another user's data.
Broken Object Property Level Authorization vulnerabilities occur when certain fields within an object should not be accessible to a particular user but are exposed through the API.
Business logic vulnerabilities arise when attackers manipulate workflows by executing legitimate operations in unintended sequences. These attacks may involve bypassing approval processes, manipulating transaction flows, or exploiting inconsistencies in multi step interactions.
These vulnerabilities share a common characteristic. They are not simple input validation errors. They emerge from the relationships between identities, objects, and application workflows.
Detecting them requires observing how systems behave under realistic interactions.
Semantic Runtime Validation is designed precisely for this purpose.
How Semantic Runtime Validation Works
Semantic Runtime Validation begins by observing how an application exposes functionality through APIs and service interfaces.
From these interactions, the system constructs a behavioral model representing identities, resources, and relationships between them. This model forms a graph of application behavior.
Once the model is constructed, the system explores possible interactions within this behavioral graph.
Requests observed under one identity may be replayed under another identity to test whether authorization rules are enforced correctly. Objects discovered during exploration may be accessed through alternative workflows to determine whether ownership constraints hold. Multi step sequences of operations may be rearranged to test whether business processes can be manipulated.
This exploration process is similar to how attackers probe systems to discover weaknesses. The difference is that the exploration is systematic and automated.
When the system discovers a path that violates expected security rules, it records the full exploit path along with reproduction steps and impact analysis.
Because vulnerabilities are reported only when exploitation is demonstrated, the resulting findings represent real security risk rather than theoretical weaknesses.
Why Semantic Runtime Validation Reduces False Positives
One of the most significant challenges in application security today is signal to noise ratio.
Traditional scanning tools frequently generate large numbers of alerts. Security teams must spend considerable time triaging results to determine which findings represent real risk.
Many organizations accumulate thousands of open vulnerability reports that are difficult to prioritize.
Semantic Runtime Validation approaches this problem differently. Instead of identifying potential weaknesses based on patterns, it attempts to validate whether those weaknesses can actually be exploited.
A vulnerability is reported only when the system demonstrates that an attacker can access data or perform operations that violate authorization rules.
This dramatically improves signal quality. Security teams receive fewer findings, but those findings represent issues that genuinely require remediation.
The shift from theoretical detection to exploit validation allows security programs to focus on the vulnerabilities that matter most.
Continuous Security Validation for Modern DevOps
Modern development practices emphasize rapid iteration and continuous delivery. Application architectures evolve continuously as new services are deployed and APIs change.
Security validation must therefore operate continuously as well.
Semantic Runtime Validation can be integrated across multiple stages of the development lifecycle.
During development, it can validate APIs before new features are released. Within CI and CD pipelines, it can automatically test application builds for authorization and workflow vulnerabilities. In staging environments, it can perform comprehensive behavioral validation prior to deployment.
Even after systems reach production, periodic validation can verify that evolving application behavior continues to enforce the intended security model.
This continuous approach aligns application security with the pace of modern software delivery.
Semantic Runtime Validation and the Next Generation of AppSec
Application security is gradually shifting from vulnerability detection toward behavioral validation.
Security leaders increasingly recognize that scanning code for patterns cannot fully answer the most important question. Can this system actually be exploited?
Answering that question requires testing how applications behave during real interactions across APIs, services, and identities.
Semantic Runtime Validation represents a natural evolution of application security testing. By modeling relationships between identities, objects, and workflows, it allows organizations to detect vulnerabilities that emerge from application behavior.
As software systems continue to grow more distributed and API driven, validating behavior will become an essential component of secure by design development.
How Aptori Applies Semantic Runtime Validation
The Aptori platform applies Semantic Runtime Validation to automatically explore the behavior of applications and APIs.
By modeling identity relationships, object ownership, and application workflows, Aptori can uncover exploitable vulnerabilities such as Broken Object Level Authorization, business logic flaws, and cross tenant data exposure.
The platform identifies exploit paths and provides actionable remediation guidance, enabling development teams to resolve vulnerabilities quickly.
This approach helps organizations move from generating vulnerability reports to continuously validating that their applications enforce the security rules they were designed to implement.
The Future of Application Security
The next generation of application security will not be defined solely by better scanners or larger vulnerability databases.
It will be defined by the ability to validate whether systems behave securely.
Semantic Runtime Validation represents a critical step in that evolution. By focusing on application behavior rather than static patterns, it enables security teams to detect the vulnerabilities that dominate modern breaches.
For organizations building API driven systems, continuous behavioral validation is becoming an essential foundation of modern application security.
Take control of your Application and API security
See how Aptori’s award-winning, AI-driven platform uncovers hidden business logic risks across your code, applications, and APIs. Aptori prioritizes the risks that matter and automates remediation, helping teams move from reactive security to continuous assurance.
Request your personalized demo today.









