Modern applications are no longer monolithic programs executing inside a single runtime. They are distributed systems composed of APIs, microservices, identity providers, data stores, message queues, and third-party integrations. A single user request may traverse many services before completing an operation.
This architectural evolution has fundamentally changed where security failures occur — and how approaches like Semantic Runtime Validation are built to detect them.
Traditional application security tools were designed for a world where vulnerabilities lived primarily in code constructs. Static analyzers searched for unsafe input handling, memory misuse, or insecure library calls. Dynamic scanners probed endpoints with payloads designed to trigger known exploit patterns.
Those approaches still matter, but they increasingly fail to capture the actual attack surface of modern applications.
Today’s most critical vulnerabilities arise from the interaction of identities, services, objects, and workflows. Authorization inconsistencies, identity propagation failures, and business logic flaws occur not because a single function is incorrect, but because the system as a whole behaves in ways developers did not intend.
To analyze these risks effectively, security systems must reason about applications at a higher level of abstraction. They must represent the structure and behavior of the system itself.
This is the role of semantic models for application security.
A semantic model describes the application as a set of interacting entities and relationships. It captures how identities interact with objects, how data flows across services, and how authorization decisions propagate throughout the system.
Instead of analyzing individual lines of code, semantic security analysis evaluates whether the system’s behavior is consistent with its intended security model.
Why Application Security Needs Semantic Models
Code Analysis Cannot See System Behavior
In modern architectures, security decisions are distributed across multiple layers.
An API gateway may enforce authentication.
An identity provider issues tokens.
A service validates object ownership.
Another service executes the requested operation.
Each component may appear secure when examined individually. Static analysis may reveal no unsafe code. Dependency scanners may find no vulnerable libraries.
Yet the system may still allow unauthorized actions if the relationships between these components are inconsistent.
For example:
- a service assumes upstream authorization was performed
- a token contains insufficient scope information
- a downstream API trusts requests from another service without verifying identity
These failures emerge from inter-service assumptions, not code-level mistakes.
Semantic modeling addresses this problem by constructing an explicit representation of the application’s interaction topology. Security analysis can then evaluate whether the relationships between components enforce the intended security guarantees.
Application Behavior Modeling
Representing the System as an Interaction Graph
Application behavior modeling begins by observing how the system processes real interactions.
Every request reveals structural information:
- which API endpoint was called
- which identity performed the action
- which object identifiers were referenced
- which downstream services were invoked
Over time, these interactions can be represented as a graph.
Nodes represent entities such as:
- API endpoints
- services
- objects
- identities
Edges represent relationships such as:
- API invocation
- object creation
- object access
- service-to-service communication
This behavior graph provides a dynamic view of how the application actually operates.
From a security perspective, the behavior graph allows analysis of multi-step interaction paths. Instead of examining a single request, security systems can analyze sequences such as:
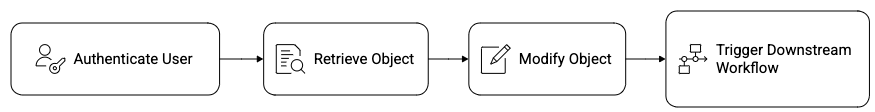
This path-oriented analysis is essential for detecting vulnerabilities such as:
- broken object level authorization
- indirect object reference abuse
- workflow bypass attacks
Traditional scanners rarely construct such graphs because they operate at the level of individual requests. Semantic behavior modeling enables security analysis across entire interaction paths.
Authorization Graphs
Modeling Permissions as Relationships
Authorization is fundamentally a graph problem.
At its core, authorization determines whether an identity is allowed to perform an action on an object.
These relationships can be represented as edges in a graph:

For example:
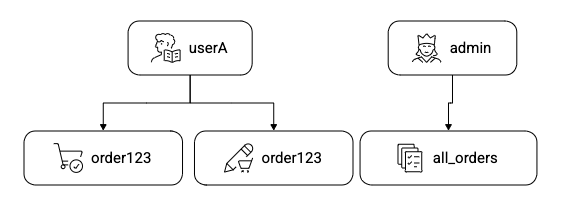
In real systems, authorization relationships become significantly more complex. Permissions may depend on:
- roles
- ownership attributes
- organizational hierarchy
- token scopes
- policy engine decisions
- service trust relationships
When these relationships are modeled together, they form an authorization graph.
Security analysis can then evaluate whether this graph contains inconsistencies.
Examples include:
• an identity that cannot read an object but can modify it
• an API that enforces ownership checks while another bypasses them
• a service that implicitly trusts upstream authorization
These inconsistencies are common in distributed systems because authorization logic is often implemented across multiple services.
Semantic models allow automated validation of the authorization graph by testing whether all edges are enforced consistently during runtime interactions.
Data Flow Models
Tracking Data Across Services
Data flow analysis has long been used in static analysis to track how inputs propagate through code.
However, in distributed systems data flows extend far beyond individual functions.
A single identifier may travel through several services before influencing a security decision.
For example:
%20-%20visual%20selection%20(1).png)
If the order identifier originates from user input and the billing service assumes it has already been validated, a security boundary may be violated.
Semantic data flow models track how data moves across service boundaries. Instead of limiting analysis to function-level flows, the model represents system-level propagation paths.
A simplified representation might look like:
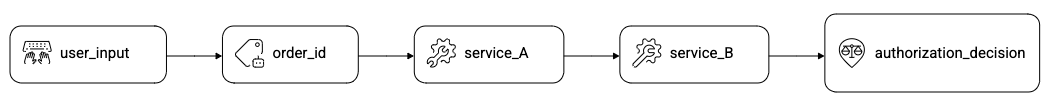
Security analysis can then evaluate whether the data influencing the authorization decision was validated correctly along the path.
This approach helps detect vulnerabilities such as:
- indirect object reference abuse
- authorization bypass through alternate APIs
- inconsistent validation across services
These issues are extremely difficult to identify through traditional static analysis because the data path spans multiple services.
Identity Propagation
Following Identity Through Distributed Systems
In distributed architectures, identity context must travel with every request as it moves across services.
Most systems propagate identity using mechanisms such as:
- JWT tokens
- OAuth access tokens
- API gateway headers
- service-to-service credentials
The expectation is that downstream services will use this identity context to enforce authorization decisions.
In practice, identity propagation is frequently inconsistent.
Common problems include:
- services trusting upstream validation without verifying identity
- identity context being dropped during asynchronous processing
- downstream services receiving only service credentials instead of user identity
These failures can create privilege escalation paths.
For example:
%20-%20visual%20selection.png)
If service_B executes operations based solely on service trust rather than user identity, the system may allow actions the user was never authorized to perform.
Semantic models capture identity propagation as part of the system’s behavior graph. Each request path records how identity information flows between services and where authorization checks occur.
Security analysis can then identify gaps where identity context is lost or improperly trusted.
Semantic Models Enable System-Level Security Analysis
Traditional security tools operate primarily at the code level. They detect vulnerabilities by matching patterns associated with known exploit techniques.
Semantic models operate at the system level.
They describe:
- how identities interact with objects
- how data flows across services
- how authorization decisions propagate
- how workflows affect system state
By capturing these relationships explicitly, semantic models allow security analysis to reason about the actual behavior of the application.
This enables detection of vulnerabilities that traditional tools struggle to identify, including:
- authorization inconsistencies
- identity propagation failures
- workflow bypass attacks
- business logic vulnerabilities
These vulnerabilities do not arise from broken syntax. They arise from broken assumptions about how systems behave.
The Future of Application Security
Modern software architectures are becoming increasingly complex. APIs connect hundreds of services. Identity systems span multiple trust domains. Workflows evolve continuously as new features are deployed.
In this environment, analyzing individual codebases is no longer sufficient.
Security validation must understand how the entire system behaves.
Semantic models provide the foundation for this approach. By representing identities, objects, data flows, and authorization relationships as structured models, security analysis can move beyond pattern detection toward system reasoning.
For developers and security engineers, this represents a fundamental shift.
Application security is no longer only about writing secure code.
It is about ensuring that the system behaves securely under all possible interactions.
And understanding that behaviour requires semantic models. Semantic Runtime Validation is the platform that operationalises this approach - making system-level semantic analysis continuous, automated, and production-ready.
Take control of your Application and API security
See how Aptori’s award-winning, AI-driven platform uncovers hidden business logic risks across your code, applications, and APIs. Aptori prioritizes the risks that matter and automates remediation, helping teams move from reactive security to continuous assurance.
Request your personalized demo today.


.jpeg)






