Application security testing has evolved significantly over the past two decades. Most development teams are familiar with Static Application Security Testing (SAST) and Dynamic Application Security Testing (DAST). These technologies have helped organizations identify many common vulnerabilities and have become standard components of secure development pipelines.
However, modern applications are no longer simple web services with a handful of endpoints. They are distributed systems composed of APIs, microservices, identity providers, and event-driven workflows. Security failures increasingly arise not from individual coding mistakes but from how systems behave when components interact.
This shift has exposed the limitations of traditional testing approaches.
A new category of analysis is emerging to address this gap: Semantic Runtime Validation. Rather than examining code in isolation or probing endpoints with generic payloads, semantic runtime analysis models how the application behaves when exercised through realistic workflows.
To understand why this matters, it helps to compare how these three approaches operate.
The Three Perspectives of Application Security Testing
Static Analysis: Understanding the Code
SAST tools analyze source code or compiled artifacts without executing the application. Their goal is to identify insecure constructs such as unsanitized inputs, dangerous function calls, insecure cryptographic usage, or vulnerable dependency interactions.
Because SAST operates directly on the codebase, it can detect issues early in the development lifecycle. Developers can receive feedback during pull requests or continuous integration runs before code reaches production.
This approach works well for vulnerabilities that have clear coding signatures. For example, static analysis can identify a SQL query that incorporates untrusted input or a function that exposes sensitive data without authorization checks.
However, SAST operates entirely within the boundaries of the code it analyzes. It does not observe how APIs interact at runtime, how identities propagate across services, or how workflows evolve across multiple requests.
In modern distributed systems, many critical vulnerabilities arise from these interactions rather than from the code itself.
Dynamic Analysis: Observing Running Systems
DAST tools interact with a running application and attempt to identify vulnerabilities by sending requests designed to trigger exploit conditions. These scanners crawl the application, discover endpoints, and attempt payloads associated with common attack techniques.
Dynamic analysis has the advantage of observing the system in a realistic execution environment. It can detect issues such as injection flaws, exposed endpoints, misconfigurations, or improper input validation.
However, DAST tools typically operate using payload-driven testing strategies. They attempt variations of malicious inputs and observe whether the application responds in a way that suggests a vulnerability.
This approach works well when vulnerabilities are triggered by specific payloads.
It becomes far less effective when vulnerabilities arise from logical interactions across multiple requests, such as authorization bypasses or workflow manipulation. DAST tools often struggle to model the stateful behavior of applications or understand relationships between identities, objects, and workflows.
As a result, many of the most damaging vulnerabilities remain invisible to dynamic scanners - contributing directly to developer trust erosion in security tooling, and to the broken economics of AI-era AppSec.
Semantic Runtime Validation: Modeling System Behavior
Semantic Runtime Validation takes a fundamentally different approach. Instead of focusing only on code constructs or malicious payloads, it analyzes how the application behaves when exercised through realistic interactions.
This approach constructs a semantic model of the system that includes:
- identities interacting with APIs
- objects created and referenced across workflows
- authorization relationships between actors and resources
- data flows between services
- state transitions across application workflows
By understanding these relationships, the system can evaluate whether the application behaves consistently with its intended security rules.
For example, if a user retrieves an object and then attempts to access another object belonging to a different user, semantic analysis can determine whether the system properly enforces ownership constraints. If the system allows access, the vulnerability is not merely theoretical. It represents a confirmed exploit path.
Similarly, if a workflow requires an approval step before completing an operation, semantic validation can test whether the system enforces that requirement across all possible interaction paths.
Because this analysis is rooted in runtime behavior and system semantics, it can detect vulnerabilities that traditional testing approaches cannot model.
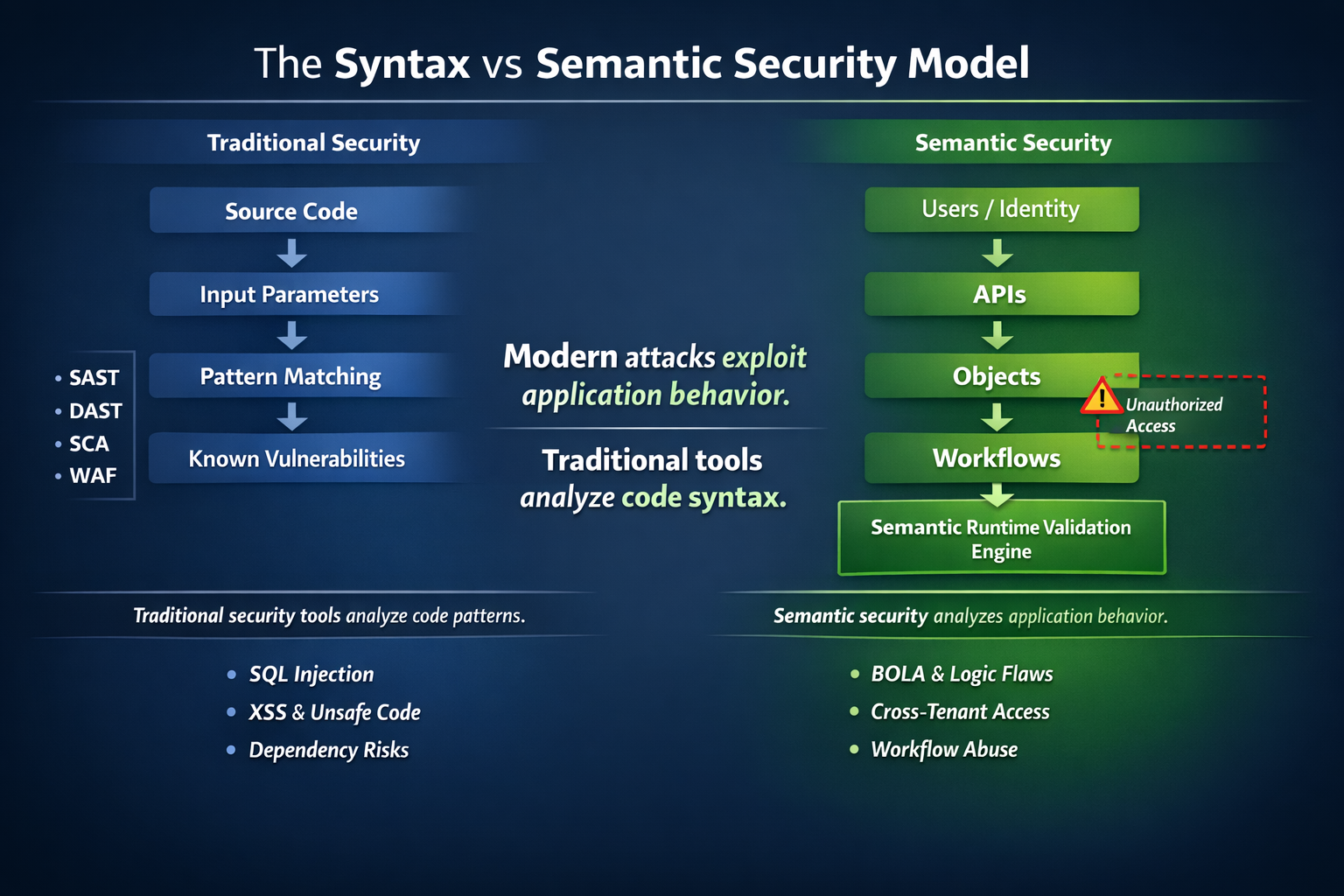
Semantic Runtime Validation analyzes application behavior and authorization logic.
Comparing the Capabilities
The differences between these approaches become clear when comparing what each method is capable of analyzing.
Static analysis excels at identifying coding mistakes but cannot confirm how the system behaves once deployed. Dynamic analysis observes runtime responses but typically lacks the context required to evaluate complex workflows.
Semantic runtime validation combines both perspectives. It analyzes the structure of the code while simultaneously evaluating how the system behaves during execution.
This allows it to identify vulnerabilities that depend on interactions across identities, objects, and workflows, rather than simple input patterns.
Why Business Logic Vulnerabilities Matter
Some of the most serious breaches in recent years have involved vulnerabilities that fall outside the detection capabilities of traditional testing tools.
Examples include:
- Broken Object Level Authorization (BOLA)
- workflow bypass vulnerabilities
- privilege escalation through indirect APIs
- transactional manipulation
- identity propagation failures in microservices
These vulnerabilities rarely involve malformed inputs. Instead, attackers exploit assumptions embedded in application logic.
They may skip workflow steps, replay requests under different identities, or invoke APIs in unexpected sequences. Each individual request may appear legitimate. The vulnerability emerges only when those requests are evaluated in context.
Traditional tools rarely understand that context.
Semantic runtime validation is designed specifically to model it.
Moving From Detection to Validation
The evolution from SAST to DAST to semantic runtime analysis reflects a broader shift in application security.
Earlier tools focused on detecting weaknesses in code. Later tools began probing applications for exploitable behavior. The next generation of security analysis aims to validate whether the system as a whole behaves securely under realistic interactions.
For developers and security teams, this means security testing must evolve beyond scanning individual components.
Modern applications require validation of:
- identity relationships
- object ownership rules
- workflow constraints
- authorization consistency across services
These are the areas where real-world vulnerabilities now occur.
Why Application Security Must Evolve
SAST analyzes code. DAST probes running applications. Both approaches were designed for earlier generations of software where vulnerabilities were primarily coding mistakes.
Modern applications are different. They are API-driven, distributed, and governed by identity, authorization, and multi-step workflows. Many critical vulnerabilities now arise from how systems behave at runtime, not from insecure syntax in code.
Semantic Runtime Validation addresses this shift. By modeling identities, objects, workflows, and authorization relationships, it verifies whether the application enforces its intended security rules during real interactions.
In modern architectures, security is no longer just about analyzing code.
It is about validating system behavior.
For the measurement framework that translates this into business outcomes, see the AppSec ROI Framework.
Take control of your Application and API security
See how Aptori’s award-winning, AI-driven platform uncovers hidden business logic risks across your code, applications, and APIs. Aptori prioritizes the risks that matter and automates remediation, helping teams move from reactive security to continuous assurance.
Request your personalized demo today.


.jpeg)






