Modern applications are evolving fast.
What used to be APIs are now becoming ecosystems of tools, agents, and AI-driven workflows. At the center of this shift is the Model Context Protocol (MCP), which enables LLMs to interact with real systems through structured tool calls.
But here is the problem.
Most MCP servers today are built like demos. They work in isolation, assume well-behaved inputs, and lack the controls required for production environments.
That approach does not scale.
If MCP is going to power real systems, it needs to be treated like any other critical backend service. That means security, observability, and behavior validation must be built in from the start.
This guide walks through five best practices for building MCP servers that are secure, scalable, and production-ready.
What is an MCP Server?
An MCP server is a system that exposes tools that AI agents and LLMs can call to interact with applications, databases, and services.
Think of it as:
- An API layer for AI agents
- A bridge between LLMs and real-world systems
- A control plane for tool execution
Unlike traditional APIs, MCP servers are driven by model behavior. This introduces a new challenge.
You are no longer just validating requests. You are controlling how an AI system interacts with your entire application.
What Are MCP Server Best Practices?
To build a secure MCP server, developers should validate all inputs, enforce authorization at the tool level, design explicit and single-purpose tools, add full observability for every tool call, and validate application behavior rather than just requests. These practices prevent vulnerabilities like unauthorized data access, tool misuse, and workflow abuse in AI-driven systems.
1. Validate All Inputs (Never Trust the LLM)
LLMs are not reliable input generators. They can produce malformed, unexpected, or adversarial inputs.
If your MCP server trusts those inputs, you are effectively exposing your system to injection and abuse.
Unsafe Example
def get_user(user_id: str):
return db.execute(f"SELECT * FROM users WHERE id = '{user_id}'")
Secure Example
from pydantic import BaseModel, Field
class UserRequest(BaseModel):
user_id: str = Field(pattern=r"^[a-zA-Z0-9_-]+$")
def get_user(req: UserRequest):
return db.execute(
"SELECT * FROM users WHERE id = %s",
[req.user_id]
)
Best Practice
- Validate all inputs using schemas
- Use parameterized queries
- Treat LLM output as untrusted input
2. Enforce Authorization in Every Tool
Authentication alone is not enough. Authorization must be enforced inside each tool.
This is critical for preventing vulnerabilities like Broken Object Level Authorization (BOLA).
Vulnerable Pattern
def get_invoice(invoice_id: str):
return db.execute("SELECT * FROM invoices WHERE id = %s", [invoice_id])
Secure Pattern
def get_invoice(context, invoice_id: str):
user_id = context.auth.user_id
return db.execute(
"SELECT * FROM invoices WHERE id = %s AND owner_id = %s",
[invoice_id, user_id]
)
Best Practice
- Always bind access to identity
- Never expose direct object lookups
- Assume the LLM may attempt unintended access paths
3. Keep Tools Simple and Explicit
Ambiguity is the enemy of reliable systems.
If your tools are unclear, LLMs will misuse them.
Avoid This
def search(query: str):
...
Prefer This
def search_users(name: str): ...
def search_orders(order_id: str): ...
def search_accounts(account_id: str): ...
Explicit Tool Schema
tools = [
{
"name": "search_users",
"description": "Search users by exact name",
"input_schema": {
"type": "object",
"properties": {
"name": {"type": "string"}
},
"required": ["name"]
}
}
]
Best Practice
- One tool, one responsibility
- Define strict schemas
- Avoid hidden or dynamic behavior
4. Add Logging and Observability
You cannot secure what you cannot see.
Every MCP server should log tool usage, including:
- Tool name
- Arguments
- User identity
- Execution time
Example
import time
import logging
def log_tool_call(tool_name, args, user_id):
start = time.time()
result = execute_tool(tool_name, args)
duration = time.time() - start
logging.info({
"tool": tool_name,
"user": user_id,
"args": args,
"duration": duration
})
return result
Best Practice
- Log every tool call
- Track identity context
- Monitor for anomalies
5. Validate Behavior, Not Just Inputs
This is the most important and most overlooked principle.
Most systems validate inputs. Very few validate behavior.
Example Attack Flow
- User signs up
- LLM retrieves user data
- LLM modifies an ID
- LLM accesses another user’s data
- Data is exfiltrated
All inputs are valid. The behavior is not.
Guardrail Example
def validate_access(context, resource_owner_id):
if context.auth.user_id != resource_owner_id:
raise PermissionError("Unauthorized")
Best Practice
- Validate identity-to-object relationships
- Enforce workflow constraints
- Test real-world usage patterns
Why MCP Server Security Matters
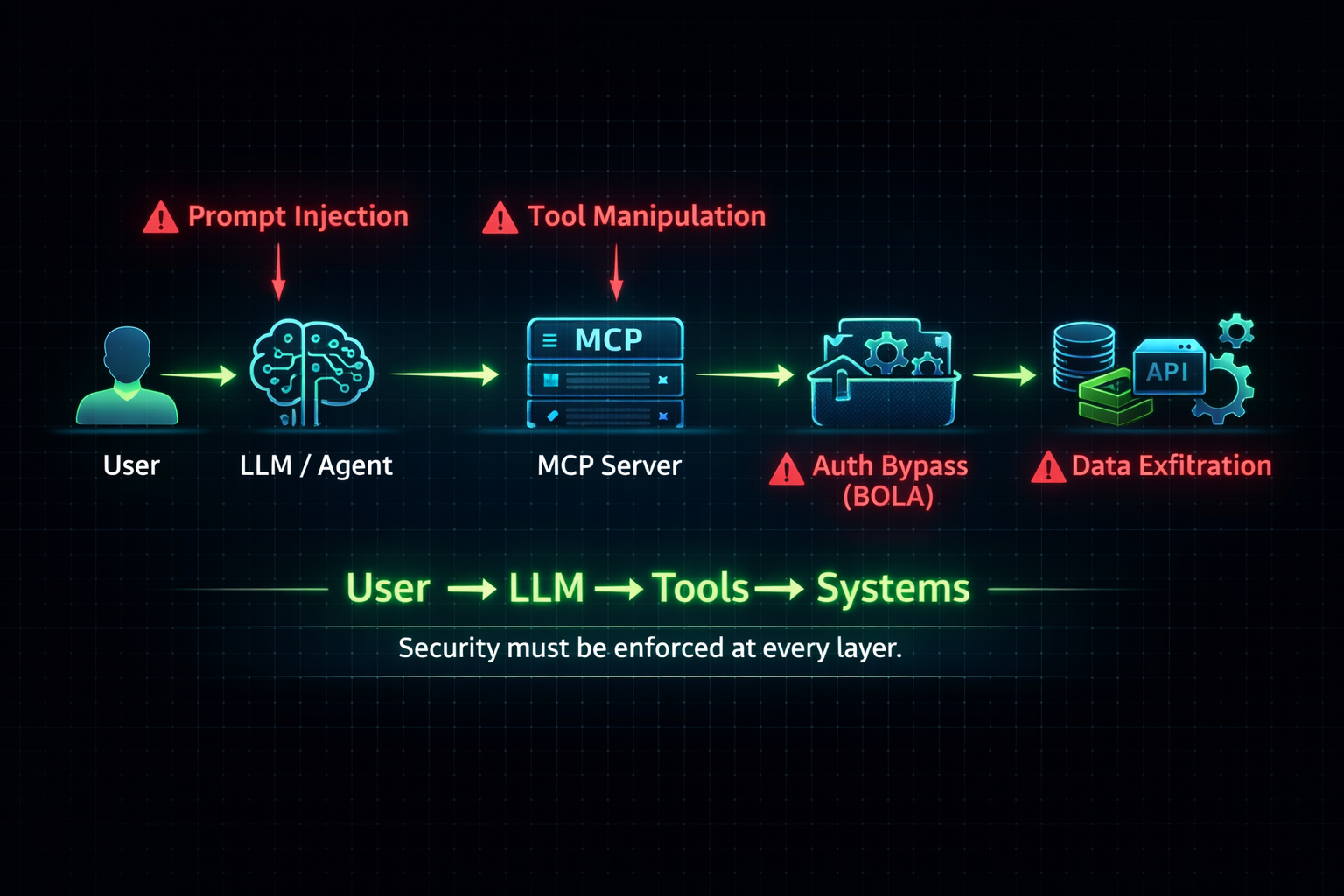
MCP servers introduce a new execution model:
User → LLM → Tools → Systems
This creates new classes of risk:
- Tool misuse
- Authorization bypass
- Cross-tenant data exposure
- Workflow abuse
Traditional tools like WAFs, SAST, or DAST were not designed for this model.
From API Security to AI System Security
This is a fundamental shift.
Security is no longer about scanning endpoints. It is about understanding how systems behave under real interactions.
This is where approaches like semantic runtime validation come in.
Instead of looking for known patterns, they:
- Model identities and relationships
- Explore application behavior
- Validate workflows dynamically
This is especially important for MCP-driven systems, where behavior defines risk.
Final Thoughts
Building an MCP server is easy.
Building a secure, production-grade MCP server requires discipline.
If you take one thing away from this guide, it should be this:
Do not trust inputs. Do not trust workflows. Validate everything.
What is an MCP server?
An MCP server exposes tools that AI agents and LLMs use to interact with applications and services.
Why are MCP servers a security risk?
Because they allow indirect access to systems through LLMs, enabling tool misuse, authorization bypass, and workflow abuse.
How do you secure an MCP server?
By validating inputs, enforcing authorization, designing clear tools, adding observability, and validating system behavior.
Take control of your Application and API security
See how Aptori’s award-winning, AI-driven platform uncovers hidden business logic risks across your code, applications, and APIs. Aptori prioritizes the risks that matter and automates remediation, helping teams move from reactive security to continuous assurance.
Request your personalized demo today.







%20(1).png)

