For many organizations, security strategy begins with a checklist.
PCI DSS.
SOC 2.
ISO 27001.
NIST.
HIPAA.
Security teams implement controls, deploy scanners, generate reports, and collect evidence for the next audit cycle. When the audit is completed successfully, the organization often declares victory. From the perspective of governance and regulatory reporting, this makes sense. Passing the audit demonstrates that the organization has implemented the controls required by the applicable framework.
But attackers do not care whether an organization passed its last compliance review.
They care whether the system can be exploited.
This gap between audit success and real security is one of the most persistent structural problems in modern cybersecurity programs. Compliance frameworks are designed to verify that certain controls exist. They are not designed to prove that those controls actually prevent exploitation.
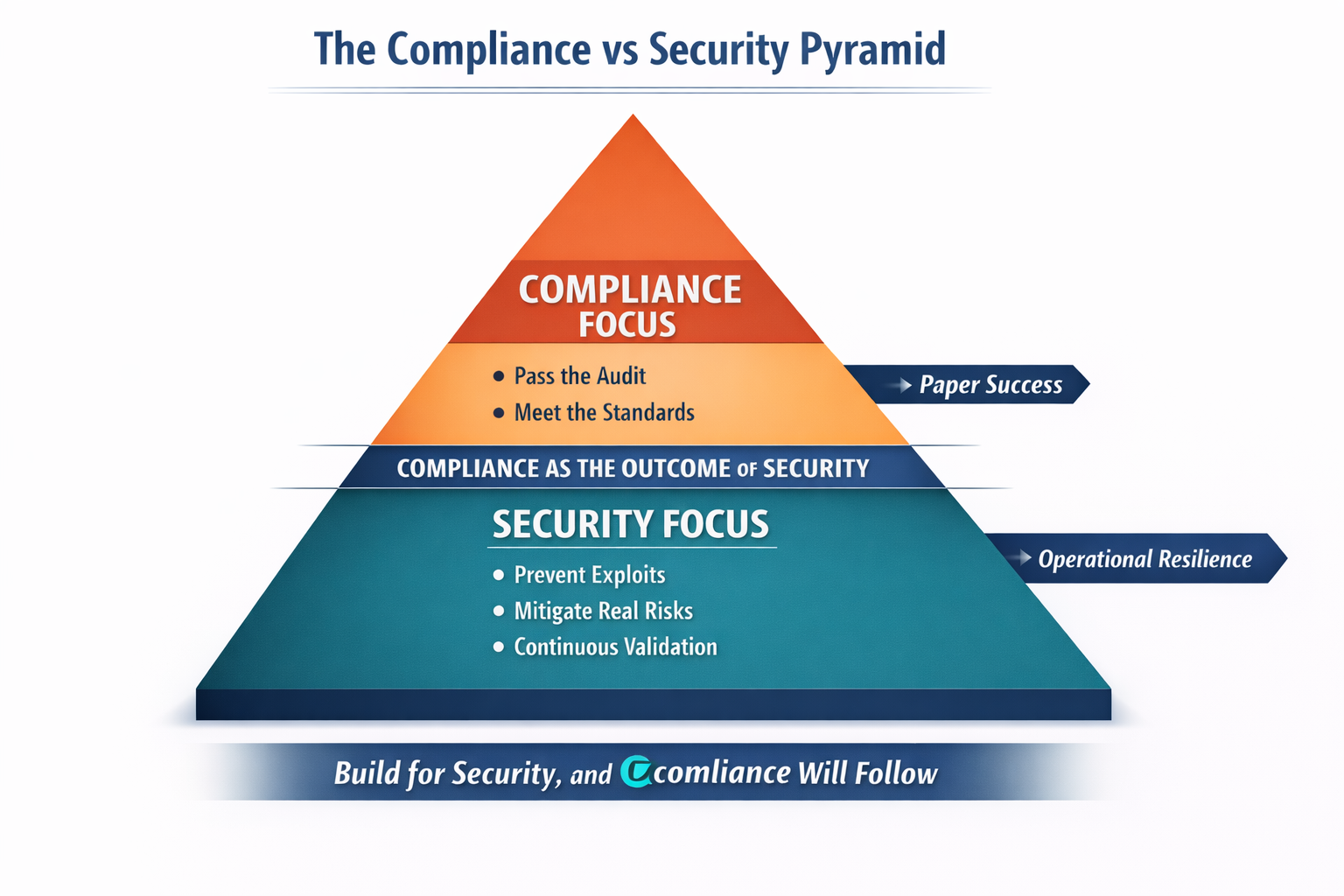
When organizations treat compliance as the objective rather than the result, security programs become optimized for producing documentation rather than reducing risk.
A stronger approach reverses the relationship.
Security must come first.
Compliance should follow.
In mature organizations, compliance is not the goal of the security program. It is the byproduct of a strong one.
The Purpose and Limitations of Compliance Frameworks
Compliance frameworks serve an important role in the cybersecurity ecosystem. They establish baseline expectations for security practices and help organizations align with regulatory requirements and industry standards.
Frameworks such as NIST Cybersecurity Framework (CSF), ISO 27001, PCI DSS, and CIS Critical Security Controls provide guidance on fundamental practices including access control, logging, vulnerability management, and incident response.
These frameworks create a shared language for evaluating security posture across organizations.
However, they are not designed to guarantee that a system cannot be compromised.
The NIST Cybersecurity Framework itself acknowledges this distinction. NIST explicitly states that the framework provides “a structure for managing cybersecurity risk” rather than a mechanism for ensuring that systems are secure against all threats.
Similarly, the Center for Internet Security (CIS) notes that its controls represent a prioritized set of defensive actions but do not eliminate risk entirely.
Compliance frameworks answer questions such as:
- Are security controls defined and documented?
- Are vulnerability scans performed regularly?
- Are access policies enforced?
- Are logs retained and monitored?
These are important controls. But they confirm the existence of security practices, not their effectiveness.
An organization may satisfy every requirement in a compliance framework while still exposing critical vulnerabilities in its applications, APIs, and identity flows.
This is why the following statement continues to resonate among security leaders:
Compliance does not prevent attacks.
Evidence of the Compliance–Security Gap
Numerous studies over the past decade have illustrated the difference between regulatory compliance and real-world security outcomes.
A report by the Ponemon Institute found that a large percentage of organizations suffering data breaches had already passed compliance audits prior to the incident. In many cases, the breach occurred only months after a successful audit certification.
Similarly, research from Verizon’s Data Breach Investigations Report (DBIR) consistently shows that attackers most frequently exploit application vulnerabilities, credential misuse, and misconfigurations, areas that are not always fully validated through compliance-based assessments.
The PCI Security Standards Council has also acknowledged this issue in guidance documents. PCI DSS compliance indicates that required controls are in place at the time of assessment, but it does not guarantee that systems remain secure afterward.
The reason is simple.
Compliance audits are periodic.
Modern software development is continuous.
Applications evolve daily through new features, infrastructure changes, and integrations with third-party services. Security controls that were validated during an audit may no longer reflect the actual state of the system only weeks later.
In other words, compliance represents a snapshot in time, while attackers operate in an environment that changes continuously.
The Compliance Trap
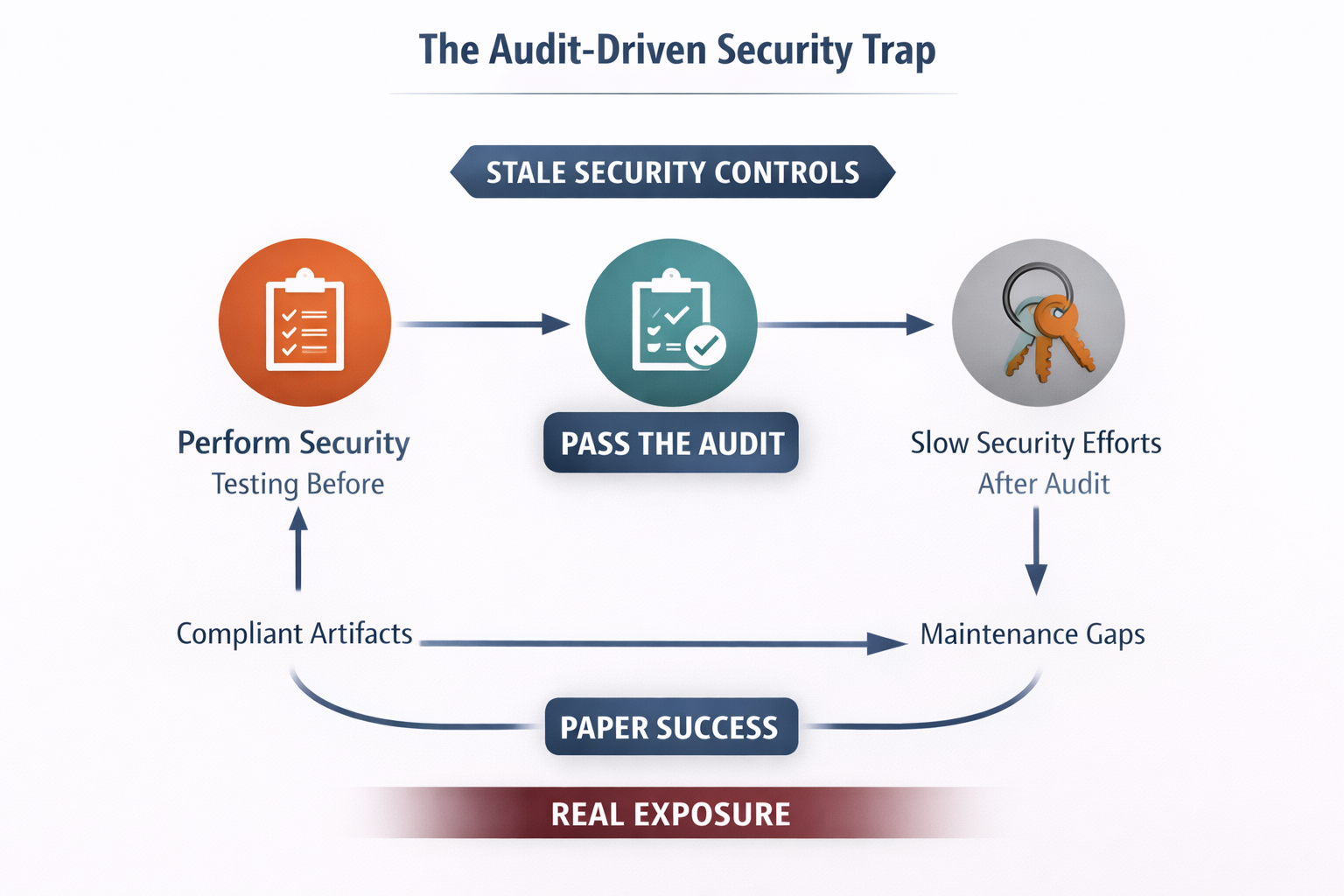
When organizations design their security programs primarily around passing audits, several structural problems tend to emerge.
Security activities begin to align with audit timelines rather than operational risk. Teams focus their testing efforts before assessment deadlines, generating reports and artifacts that demonstrate compliance. After the audit concludes, attention shifts elsewhere until the next cycle begins.
This periodic rhythm creates long windows during which vulnerabilities can remain undiscovered.
Documentation also begins to replace validation. Compliance processes require evidence that controls exist and are functioning. Screenshots of scan results, configuration exports, and policy documents become the primary artifacts used to demonstrate compliance.
But evidence that a tool was executed is not the same as evidence that the system is secure.
In many environments, developers also begin to experience security as a compliance exercise rather than a protective discipline. Security tickets appear primarily when audits approach, often driven by automated scanning tools that generate large volumes of alerts. When many of these alerts turn out to be false positives or low-risk issues, developer trust in security tools begins to erode.
Over time, the security program becomes focused on satisfying external requirements rather than understanding the organization’s true attack surface.
The Nature of Modern Application Risk
One of the reasons compliance-centric security struggles today is that modern applications are fundamentally different from the systems that many security frameworks were originally designed to evaluate.
Modern software is composed of APIs, microservices, identity providers, cloud infrastructure, and distributed data services. These systems interact through complex authorization rules and workflow relationships.
Many of the most damaging vulnerabilities in modern applications arise not from simple coding errors but from behavioral flaws.
These include:
Broken Object Level Authorization (BOLA)
Broken Object Property Level Authorization (BOPLA)
Business logic manipulation
Workflow abuse
Privilege escalation across services
These types of vulnerabilities are difficult to detect using traditional scanning techniques that rely on pattern matching.
They emerge from how systems behave when identities, objects, and workflows interact during real usage.
The OWASP API Security Top 10 highlights this shift clearly. Broken authorization flaws such as BOLA consistently rank as the most common and most impactful API vulnerabilities across industries.
Detecting these vulnerabilities requires analyzing how an application behaves when real interactions occur, not simply whether certain code patterns appear in the source code.
From Detection to Validation
Traditional security tools often focus on identifying potential weaknesses.
Static analysis tools scan code for insecure constructs.
Dynamic scanners probe endpoints for injection signatures.
Penetration tests simulate attacks within a limited engagement window.
These methods are valuable, but they frequently produce large numbers of theoretical findings.
What security teams increasingly need is the ability to determine which vulnerabilities are actually exploitable.
Proof-of-exploit validation provides this critical layer of context. Instead of reporting that a potential weakness exists, the system demonstrates that the vulnerability can be triggered through real application interactions.
This dramatically reduces noise while allowing security teams to focus on the issues that represent genuine risk.
Research from Google’s Project Zero and other vulnerability analysis groups consistently emphasizes that exploitability is the factor that determines real-world impact. A theoretical vulnerability may never be exploited, while a subtle authorization flaw can lead to catastrophic breaches.
Security programs that prioritize exploitability over theoretical detection are able to remediate the most important issues faster.
Compliance as the Natural Outcome
When organizations build their security programs around continuous validation and exploitability analysis, something important happens.
Compliance becomes easier.
Continuous security testing produces operational evidence automatically. Controls are validated through real activity rather than documentation. Security teams spend less time preparing artifacts for auditors because the evidence of security practices already exists within the system’s operational data.
Instead of building security programs specifically to pass audits, organizations simply demonstrate that their existing security practices satisfy the requirements of the relevant frameworks.
Compliance becomes a reporting exercise rather than a primary driver of the security program.
This shift aligns with the philosophy expressed in many modern security frameworks. The NIST CSF 2.0 update, for example, emphasizes governance, risk management, and continuous monitoring rather than static compliance validation.
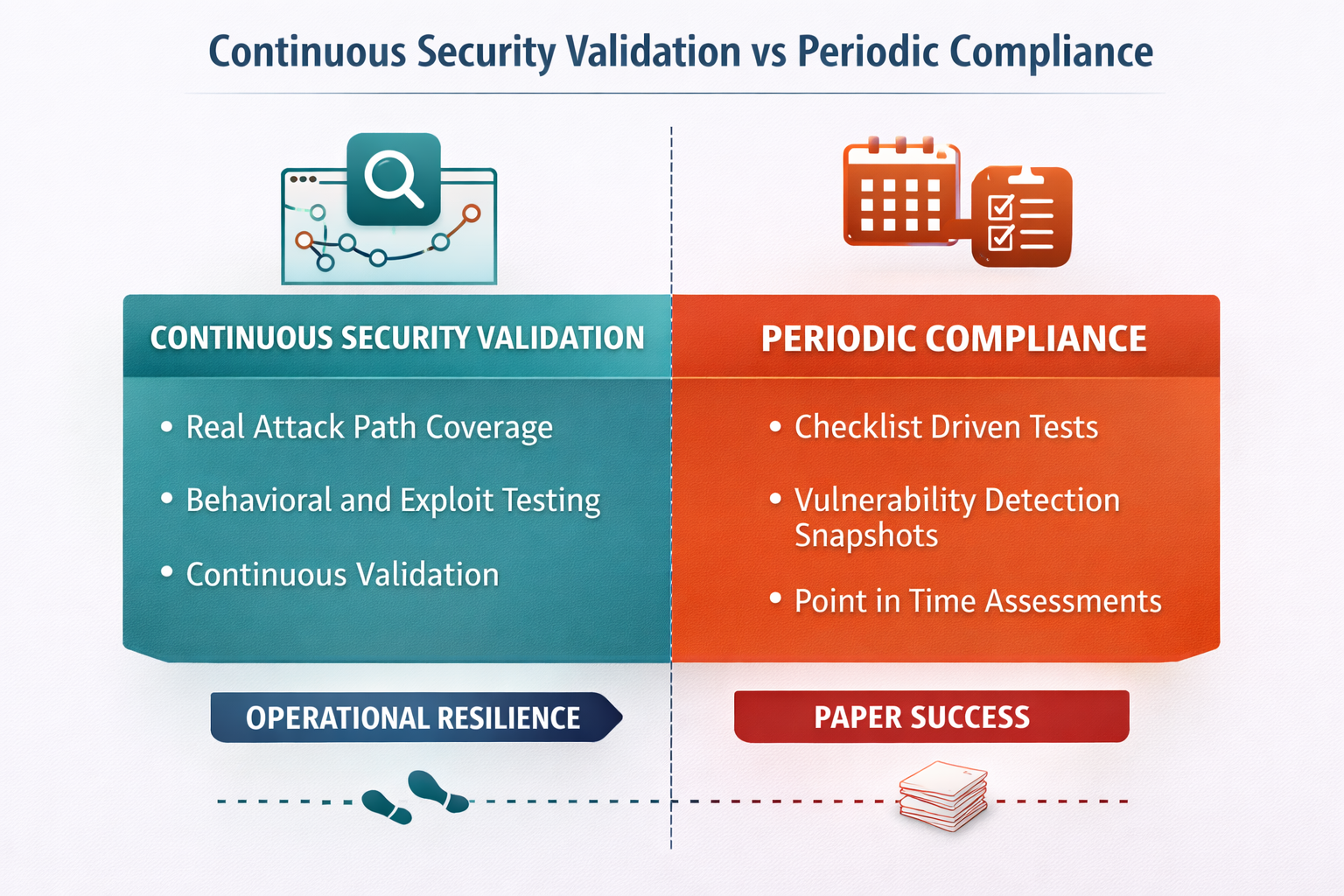
A Shift Toward Continuous Security Validation
As software development accelerates and application architectures grow more complex, many security leaders are rethinking how security validation should be performed. Periodic testing and compliance-driven assessments cannot keep pace with continuous software delivery.
The emerging model focuses on continuous security validation, where applications are tested dynamically as they evolve. Rather than relying solely on pattern-based scanners, this approach evaluates how systems behave under real interactions to determine whether vulnerabilities can actually be exploited.
Technologies such as semantic runtime validation help enable this shift. By modeling identities, objects, APIs, and service interactions, these systems can explore real execution paths and uncover authorization failures, business logic vulnerabilities, and API abuse conditions that traditional tools often miss.
Platforms such as Aptori apply semantic runtime validation to continuously test application behavior, identify exploitable attack paths, and provide proof-of-exploit evidence. The result is a security program focused on validating resilience rather than generating reports. When systems are proven to resist exploitation, compliance naturally becomes the outcome of security rather than the objective.
Final Thought
Compliance frameworks are valuable tools for establishing security baselines.
But they were never intended to prove that systems are secure.
Organizations that build their security programs around passing audits often end up with extensive documentation but limited visibility into real attack paths.
Organizations that build their programs around understanding and preventing exploitation achieve a different outcome.
They reduce real risk.
They improve developer trust in security processes.
And they satisfy compliance requirements almost automatically.
Security should be the objective.
Compliance should be the outcome.
References
NIST Cybersecurity Framework (CSF)
https://www.nist.gov/cyberframework
Verizon Data Breach Investigations Report (DBIR)
https://www.verizon.com/business/resources/reports/dbir/
OWASP API Security Top 10
https://owasp.org/www-project-api-security/
PCI Security Standards Council Guidance
https://www.pcisecuritystandards.org/
Center for Internet Security Controls
https://www.cisecurity.org/controls
Ponemon Institute – Cost of a Data Breach Report
https://www.ibm.com/reports/data-breach
Take control of your Application and API security
See how Aptori’s award-winning, AI-driven platform uncovers hidden business logic risks across your code, applications, and APIs. Aptori prioritizes the risks that matter and automates remediation, helping teams move from reactive security to continuous assurance.
Request your personalized demo today.









